Where can I find the SDK for the Enterprise Wi-Fi Radios? If there is no SDK available for download in the product's Software Downloads section then the SDK will be in the release .zip folder.
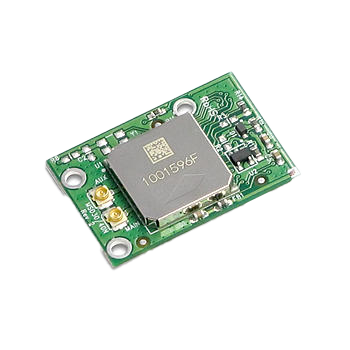
30 Series 802.11a/b/g Wi-Fi 60-pin pluggable module
Browse Certifications and Documentation in our Support & Documentation Center.
| Distributor | Part | In Stock | Region | Buy |
|---|---|---|---|---|
| Mouser Electronics | MSD30AG | 0 | North America | Buy Now |
Where can I find the SDK for the Enterprise Wi-Fi Radios? If there is no SDK available for download in the product's Software Downloads section then the SDK will be in the release .zip folder.
1) The SD host controller driver (their driver, not ours) detects that a device is on the SDIO bus and signals the SD bus driver (a Microsoft driver) 2) The SD bus driver enumerates the card to determine what device it is and what client driver needs to be loaded. The bus driver does this at a low clock frequency because it doesn?t yet know what bus speed the client device can support. Note that the host controller driver is the one that actually performs all accesses to the card as it is the one that manages the actual SDIO controller hardware on the host platform. The bus driver is accessing the card via the host controller driver. 3) The SD bus driver determines that our driver is the ?client driver? registered for the card by reading the vendor/product IDs from the card and looking up that information in the registry. Our driver is registered for that combination of VID/PID. 4) The bus driver loads the client driver, which in this case is our driver. 5) The client driver continues initialization, which includes accessing the card itself by making calls to the SD bus driver which passes those calls on to the host controller driver which implements the actual card access via the host controller itself in the host CPU. It?s important to note that the client driver (us) only requests that a card access be made; it is the host controller driver that implements the access via the host controller on the host CPU. 6) Very early in the initialization sequence the client driver (us) makes a call to the bus driver to configure the bus speed, bus width etc. The speed is the lower of what the card supports and what the host controller supports on that slot. From that point on, all accesses are occurring at a much higher bus speed. 7) The card continues initialization, which includes downloading the firmware and then enabling interrupts. From this point on, interrupts have to be working for the card to function properly.
Ezurio provides 3D files (STEP) files for most but not all of it's modules. Based on the nature of the information in the files, in most cases Laird requires a login to access these files as well as layout files and software/firmware downloads. As such, for most modules, the 3D files are found under the Software Downloads tab of the product page. The page offers a credentials request link for customers who need credentials. In most cases, the credentials are provided via return email within about 10 minutes. Please contact support if you have any additional questions or have any issues accessing our downloads.
We highly do not recommend conformal coating the radio module. If you plan on encapsulating the radio module in a potting compound or conformal coating, you must assure that the compound in liquid or solid form does not enter under the shield where there are sensitive RF components. Some of the capacitive and inductance values are as low (pF and nH) and could be sensitive to contacting materials such as potting compounds. There are potting compounds and conformal coatings which have very good dielectric constants and are suitable for 2.4 GHz potting applications, however, when you apply any of these, they were not accounted for in the circuit design and might reduce performance of the device (or all together cause it not to function). You should run tests on their particular potting compound and evaluate radio's performance and range. Also, it's worth mentioning that applying any compound, conformal coating or potting directly to the module WILL void the warranty. If your application requires 100% sealing of the radio module, there is a way to do this very successfully without impacting the module performance. Simply place the module on your PCB. Place a plastic cover over the module (like a hat), make the cover large enough to cover the whole module. Apply glue around the bottom perimeter of the cover where it sits on the PCB. This allows the module to function in free air-space while there is a complete seal around it. This information is only for reference and we recommend you should conduct your own testing with your prototype of your end application to find the best suitable fit for your design.
We only recommend reflowing our modules once as it can damage the module and void the warranty.
Ezurio provides layout files PADS and PADS ASCII formats. The ASCII files will import to Altium (and Protel varients) as well as Cadence (Orcad and Allegro) CAD packages. As far as we know, there is no way to import to Eagle CAD. Please be sure to use the .asc file for PCB and the .txt file for the schematic when importing to Altium. Ezurio uses ORCAD for schematics (Gerbers).
The recommended cleanser is "hydrocarbon cleaning oil", which can be used to clean the RF shield and PCB. We do not recommend the use of alcohol as it doesn't work as well and could leave residue on the boards.
You can modify this feature by creating a new registry called ?NotifyAttempts? under ?hklm/software/Laird/ScuTray?, this allows you to disable / enable the pop-up message for WPA / WPA2 authentication and even set the number of attempts before notification. -DWORD: NotifyAttempts -Values: 0 (disabled); NOT 0 (the number of attempts before notification)
For the 30AG, we recommend the 3.5.0.9 cab build or later for both test cases. For the 40NBT, use 3.4.13.36 cab build or later. As for the 45N, cab build from 3.5.1.6 can support both test cases.
Yes, here is an example. 1. The auto profile list contains SSID_1 and SSID_2 2. Device is connected to SSID_1 3. RSSI drops below roam trigger, the radio scans for other APs and finds SSID_2 is a better candidate 4. The radio disconnects from SSID_1 and connects to SSID_2
For the 10, 15, 30, and 40 series, the status of the LCM / SCU can be in one of two states, "non-associated? and ?associated". Once the radio has associated with an AP, it will move from "non-associated? to ?associated". If WPA / WPA2 authenticates failure, the status will switch between "non-associated? and ?associated". If authentication occurs without an IP the radio cannot be identified from the status field -- you will need to check in the IP field. For the 45 and 50 series, the status in LCM / SCU can be in one of three states, "Not Associated", "Associated", and "Connected?. Associated with no IP is a valid state for our radios to attempt to reconnect with an invalid PSK. Once the radio has associated with an AP, it will move from "not associated? to ?associated". Only after the radio authenticates and has an IP will it move to the "Connnected" state. In the case of WPA or WPA2 authenticated failure or authentication without an IP the radios will remain in an "associated" state.
NDIS5 runs Laird's WEC7 release.
No, the patch that supports SHA-2 is in the Windows Embedded Compact 7 Monthly Update (April 2016). Prior to that, the OS itself doesn't support it.
Setting the following registry to 0 can achieve this: HKLM\Comm\SDCCF10G1\Parms\Configs\GlobalConfig DWORD: trayIcon - 0 = Hide Icon - Non-0 = Show Icon
The radio chipset value is written by the driver when it loads, and indicates which radio is actually installed. LCM uses this value to determine some parameters that vary between radio types. If you want to hard code the Wi-Fi radio before the driver loads, you can do so with this registry: [HKEY_LOCAL_MACHINE/Comm/SDCCF10G1/Parms/Configs/GlobalConfig] "RadioChipSet"=dword:00000006 The values for that registry key are in the sdc_sdk.h as follows: typedef enum _RADIOCHIPSET { RADIOCHIPSET_NONE = 0, RADIOCHIPSET_SDC10 = 1, //BCM4318 RADIOCHIPSET_SDC15 = 2, //BCM4322, RADIOCHIPSET_SDC30 = 3, //AR6002, RADIOCHIPSET_SDC40L = 4, //BCM4319, RADIOCHIPSET_SDC40NBT = 5, //BCM4329, RADIOCHIPSET_SDC45 = 6, //AR6003, RADIOCHIPSET_SDC50 = 7, //AR6004, } RADIOCHIPSET;
mandatory/optional input for EAP type EAP credentials Mandatory input Optional input LEAP User name, user password EAP FAST User name, user password PAC file, FAC password PEAP MSCHAP User name, user password CA cert PEAP GTC User name, user password CA cert EAP TLS User name, user cert CA cert EAP TTLS User name, user password CA cert PEAP TLS User name, user cert CA cert Note 1: this settings should be read in user perspective but not for actual implementation. For example, when a user does not input PAC file, it will use auto PAC provisioning. If a user inputs it, it will do a manual PAC provisioning. Note 2: user password is not used for TLS but only user cert is used instead.
EAP-TLS is a tunnel authentication. outer identity: this is the User-Name in the RADIUS packet and visible to all intermediate parties inner identity: this is the actual user identification. It is only visible to the user himself and the Identity Provider The user cert is issued to a user identified by the username, so the username has to be configured so we know which user cert we should be using for the authentication. By default, the username is also used during authentication as the outer identity which gets sent in the identity response packet.
There are two reasons to send out null packets with p bit enabled. 1. Its RSSI has crossed over the Roam Trigger and the client radio is supposed to start scanning for a new AP. 2. The client radio is running one of our power-save modes (Fast or Max) and is going to sleep for a brief (e.g. 20 ms) period and is telling the AP so it will buffer traffic for it while it sleeps. After a radio has slept for some period of time (defined as the interval between DTIM periods) it is supposed to wake up and indicate to the AP that it is awake by sending a null packet with the P-bit turned off. The radio should only wake if it has traffic to send or it sees from the DTIM in the AP?s beacons that the AP has traffic to send to it.
Method 1: Radio driver is asked by power manager to go to low power state Suspend/resume without cutting power to radio Method 2: Radio driver is asked by power manager to go to low power state Cut power to radio Suspend/ Resume Reapply power to radio Eject/insert radio Note 1: Method 1 is the simplest way to deal with suspend/resume, but the OEM needs to consider the current consumption of the radio at a low power state. For example, current consumption for the 40NBT is 7.7mA and for the 45N it is 200uA. Note 2 : In general, method 1 is more recommended because method 2 may cause a delay to make the radio reconnect after resume.
sdcgina.exe vs sdc_gina.exe : sdcgina.exe spawns all of the components we need (e.g. supplicant, scutray). sdc_gina.exe is a UI application that, for example, pops up when the credentials must be input.
No. 40 series radios only support the H4 protocol, not BCSP (BlueCore Serial Protocol). If the BCSP driver starts up and occupies COM port after Bluetooth initialization, the 40NBT's Bluetooth may not function properly.
The following channels require DFS in Korea KCC/KC domain. Channel Frequency MHz 52 5260 56 5280 60 5300 64 5320 100 5500 104 5520 108 5540 112 5560 116 5580 120 5600 124 5620
A list of our radios and supported connector types can be found here: WiFi + Bluetooth Modules
With EAP-MS-CHAPv2, the data sent in tunnel will be encapsulated as EAP-MESSAGE AVP (attribute-value pair). In the case of MS-CHAPv2, there is no such extra encapsulation it is just the MS-CHAPv2 message.
The attached document is the list current channels for the KCC domain as of 2015. In document, red means DFS required.
Standard: indicates PMK Caching: This means that the 802.1x authentication can be skipped on an access point that a client has already authenticated to once before. Only the 4-way handshake needs to happen. This is useful for a client that needs to reconnect to an access point that it roamed away from previously, due to signal loss etc. However, if a client has not roamed to a particular access point during its current working session, it must then authenticate to that specific access point using 802.1x. PMK Caching is the method defined in the 802.11x (WPA/WPA2) specification. Opportunistic Key Caching: With this method, a client device can skip the 802.1x authentication with an access point after a full authentication,and only needs to perform the 4 way handshake when roaming to access points that are centrally managed by the same WLC in an LWAPP or other controller-based infrastructure. This means that the client doesn't need to authenticate with access points that it wants to roam to, as long as the client has authenticated successfully to at least one of the access points in the same zone as the access point that handled the previous successful authentication. In this case, the PMK identifier has been cached at a central location, like the WLC (or wireless switch.) With OKC, the client must support this method for it to be used, even if the infrastructure has been configured with OKC enabled.
CCKM is supported with all EAP types Laird supports?LEAP, EAP-FAST, PEAP-MSCHAPv2, PEAP-GTC, PEAP-TLS, EAP-TLS and EAP-TTLS. ACS supports all of the EAP types except EAP-TTLS. However, supporting CCKM is not dependent on using ACS as the RADIUS server. Laird can do CCKM with any RADIUS server since CCKM support is in the wireless infrastructure.